In today’s interconnected and digitized business landscape, the paramount importance of safeguarding your business network cannot be overstated. Cybersecurity is no longer a choice; it’s a fundamental necessity.
The relentless evolution of cyber threats requires robust countermeasures to prevent potential breaches and data compromises that could cripple your operations and tarnish your reputation.
Introduction to Cybersecurity and Network Protection
In the digital realm, network security services function as the impenetrable fortress shielding your business from a barrage of digital adversaries.
As devices and systems become more intertwined, cybercriminals find and exploit vulnerabilities to gain unauthorized access, cause data breaches, or disrupt your operations.
Network security services are the bedrock on which your business’s integrity, trust, and continuity rest securely.
Implement Strong and Unique Passwords

Just as a fortress begins with a solid gate, digital security starts with strong passwords. These serve as the initial defense against unauthorized access.
Crafting unique passwords, akin to having distinct keys for every room, is imperative. Avoid predictable information like birthdays; instead, combine upper and lower case letters, numbers, and symbols.
Consider reputable password managers for secure storage.
Regularly Update and Patch Software
In the dynamic landscape of cyber threats, attackers constantly exploit software vulnerabilities. Regularly updating and patching applications and systems is akin to reinforcing fortress walls.
Updates frequently include security patches that fix known vulnerabilities. Neglecting updates exposes your business network to potential attacks that exploit these weak points.
The practice of software updates extends to all aspects of your business, from operating systems to office software and security applications. Automated updates can streamline this process, ensuring that your systems are always fortified with the latest defenses.
Regularly testing these updates in a controlled environment before implementing them across your network is also recommended to avoid unexpected compatibility issues.
Secure Network with Firewalls and Intrusion Detection Systems
Visualize a moat encircling your digital stronghold: Firewalls and intrusion detection systems play this role.
Firewalls erect barriers between your network and external threats, while intrusion detection systems scrutinize network traffic for suspicious activities. These layers work in tandem, deterring unauthorized access and identifying potential breaches.
Firewalls come in two main types: hardware and software. Hardware firewalls are often integrated into network routers, acting as the first line of defense between your network and the broader internet.
Software firewalls, on the other hand, are installed on individual devices and provide an additional layer of protection against both inbound and outbound threats.
Educate Employees about Phishing and Social Engineering
Even the strongest fortress crumbles if guards can be deceived. Phishing and social engineering target the human element, often the weakest link.
Educating your employees to identify and thwart these threats is crucial. Train them to recognize suspicious emails, links, or requests for sensitive information.
A vigilant workforce prevents inadvertent breaches.
Use Multi-Factor Authentication
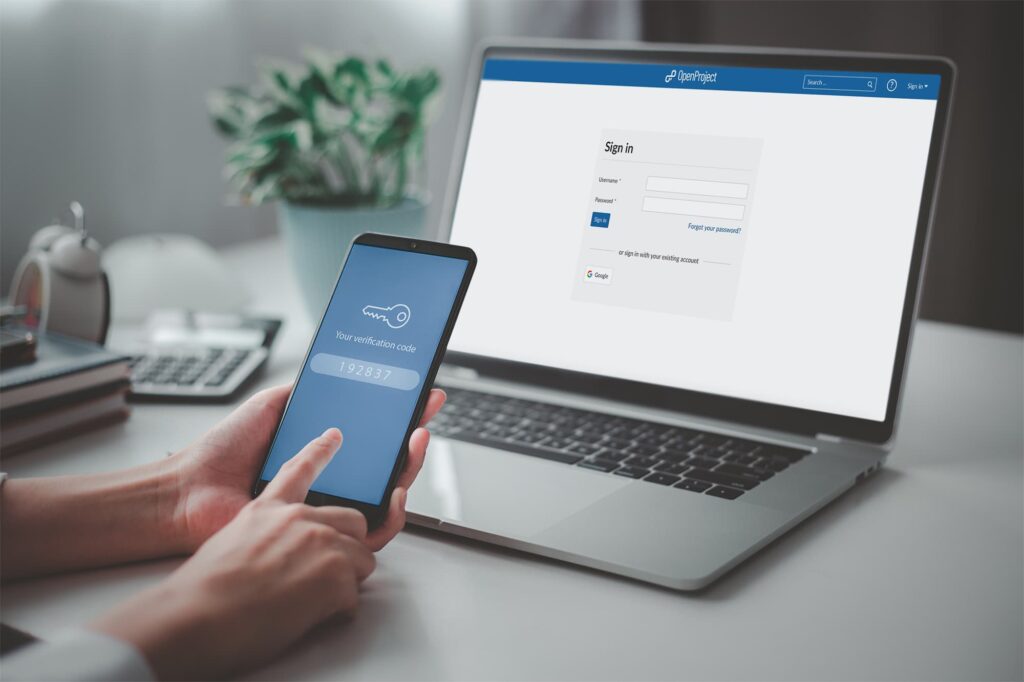
Multi-factor authentication (MFA) is equivalent to requiring multiple keys to unlock a vault. Beyond a password, MFA demands additional verification, such as fingerprints or mobile-generated codes.
Even if a password is compromised, MFA adds an extra layer of defense, rendering unauthorized access considerably more challenging.
Implementing MFA requires a combination of something the user knows (like a password), something they have (such as a smartphone), and something they are (like a fingerprint).
This multi-layered approach significantly reduces the likelihood of unauthorized access, even if an attacker manages to obtain one of the authentication factors.
Backup Critical Data
Consider a concealed chamber within your fortress, harboring your most precious assets. Regularly backing up crucial data mirrors securing these treasures in alternate locations. Ransomware attacks or data breaches might lead to data loss.
With backups, you can swiftly restore operations without succumbing to ransom demands.
The 3-2-1 backup strategy is a recommended approach: maintain three copies of your data, store them on two different media types, and ensure that one copy is stored off-site.
This strategy safeguards against various risks, including hardware failures, natural disasters, and cyberattacks. Regularly testing your backups to ensure their integrity is equally crucial.
Restrict Employee Access
Not all areas within a fortress are accessible to everyone. Similarly, employees don’t require universal access to your business network.
By configuring access controls based on roles, you minimize damage from insider threats or accidental data exposure. Limiting access fortifies your defenses.
Access control can be achieved through user permissions, role-based access, and the principle of least privilege (POLP).
POLP ensures that employees have access only to the resources and information necessary to perform their tasks. This minimizes the potential impact of a compromised account.
Monitor Network Traffic
Think of surveillance cameras throughout your fortress; monitoring network traffic is its digital equivalent.
Vigilant monitoring detects anomalies or patterns hinting at a breach. Early detection permits swift containment and damage limitation, bolstering your defense strategy.
Advanced security information and event management (SIEM) systems can assist in monitoring network traffic effectively. These systems aggregate and analyze data from various sources, enabling the identification of unusual or suspicious activities.
Regularly reviewing these insights helps maintain a proactive stance against potential threats.
Create an Incident Response Plan
Even the most fortified fortress anticipates unforeseen events. In cybersecurity, this is your incident response plan.
It outlines steps to take during a breach. A comprehensive plan covers containment, investigation, communication, and recovery. Preparedness ensures efficient threat mitigation, minimizing operational impact.
An incident response plan should be a dynamic document, regularly reviewed, updated, and tested through simulated exercises.
In the event of a breach, having a well-documented plan in place can significantly reduce the time it takes to identify and mitigate the threat, minimizing potential financial and reputational damage.
Stay Informed about Cybersecurity Trends
An unwavering fortress remains updated on enemy strategies. In the ever-changing realm of cybersecurity, threats evolve swiftly.
Subscribing to security newsletters, attending webinars, and participating in industry discussions provide insights into emerging risks and best practices.
Conclusion

In conclusion, safeguarding your business network isn’t optional—it’s imperative. Employing these cybersecurity best practices construct a robust fortress shielding your business from ever-evolving cyber threats.
Similar to fortress upkeep, cybersecurity demands ongoing attention to counter new challenges. An adequately shielded network is pivotal for a thriving, resilient business in the digital era.
As technology advances, cyber threats follow suit. Stay proactive, update strategies, and seek professional guidance to maintain a strong cybersecurity posture. Your business’s future relies on it.



